The demands of market security in cloud environments are clear: the highest level of security possible for data and applications, compliance with all certifications and standards required and a clear and simple management that does not require investing much time.
To cover all these needs, the major cloud providers include all these tools on their platforms by default. In today's post, we will see some of them.

IAM Identity & Access Management
These tools provide the necessary functionality to manage identity and access. They allow the creation of different policies for each user or group according to the needs of the organisation.
In this way, the security teams can apply the basic recommendations in the management of privileges: the separation of functions and the principle of the minimum privilege. With this level of granularity, each user can perform only the strictly necessary operations, according to their roles, without the need to use other external tools.

You can control the time of the day a user can access an API, from which IP he does it or whether he uses SSL. It is possible to enable access for mobile applications or browsers by temporary security credentials that guarantee access only to specific resources during a configurable period of time.
They also allow to grant federated access to employees and applications to the console, services, or APIs using other external systems such as Active Directory. In addition, they support SAML 2.0 to use third-party identity management solutions.
An IAM allows centralised management of all security credentials and permissions so that each user can be assigned access only to the resources that are assigned to them. In contrast to traditional solutions, it provides much more visibility and helps to abandon poor practices such as sharing passwords, not changing them regularly or allocating more permissions than necessary.
Multifactor authentication
Another extra feature included, at no additional cost on cloud platforms, is multifactor authentication. It can be enabled to control access both at the account level and for individual users through various access methods (certificates, tokens, SMS codes).
Anyone with the appropriate privileges can use any of the approved multifactor access methods to manage access to sensitive resources or services.

Key management
It is quite common that there is some concern about the physical location of the data. If these are on-premise or if they are stored in a certain region provides the peace of mind of being compliant with a certain regulation.
But the technological reality is that it is the permissions on that data that determines that they can be seen or used from a certain place, this is what some have called logical location.
A key aspect to control access to information is the use of cryptographic keys. These keys must be carefully controlled to prevent unlawful access to any account, especially those of administrative users. The management and monitoring of these keys must be ensured in the platform through specific tools.
Fully managed services such as Cloud KMS and AWS KMS allow you to generate, import your own keys, use, rotate and destroy encryption keys, as well as define usage and permissions policies.
These services are fully integrated with Cloud Audit Logging or AWS CloudTrail to have logging and audit so that you can monitor how these keys are being used to be sure accounts with privileges are not compromised. In addition, they guarantee compliance with several compliance programs.
Latest news
At its latest re:Invent, Amazon joined the new trend started by Google and other providers and introduced a new tool to facilitate control, administration and multiple account security.
This service is based on the use of organisations, so it is called AWS Organizations and allows you to create groups of cloud accounts to manage security settings.
What advantages does it offer?
- Manage multiple accounts centrally.
- Control what AWS services are available to individual accounts.
- Create custom policies that can be applied to users and groups to manage security.
- Centrally control the use of services in multiple accounts.
- Automate the creation of new accounts.
- Simplify billing.
In addition, they incorporate automatic protection services against DDoS to protect the applications executed in the public cloud. Amazon offers its new AWS Shield product free of charge with automatic online mitigation and always-on detection to minimise downtime and application latency.
Google provides, by default, automatic protection against most DDoS attacks of level 4 when using load balancing through a proxy, it absorbs most of the attacks on their Frontend infrastructure to prevent them from reaching the clients’ computing instances, private network isolation and virtual network isolation.
One of the new features presented by Google in Next is Data Loss Prevention API, which automatically discovers sensitive data and helps to classify them.
It detects and classifies, in both text and images, data such as:
- Credit card numbers.
- Social security numbers.
- Passport numbers.
- Numbers of driving licenses.
- Phone numbers and many
In addition, it can alert users when they are going to save sensitive data in applications. It allows, before that data is written to disk, to automatically choose the most appropriate storage system and the correct set of access controls. All this to have identified and know where and how are stored the most sensitive data of an organisation.
Have you got all these security tools on-premise?
As we have seen, in the public cloud we have more and more tools to guarantee, by default, the security of applications and data.
From solutions for identity management, multifactor access, key management services that allow you to use your own keys, tools for auditing, products to better organise resources or to automatically protect our contents.
It is not necessary to make an extra payment or spend weeks installing and configuring new tools, they are already included to start working with maximum security and thus meet the current demands of the market.
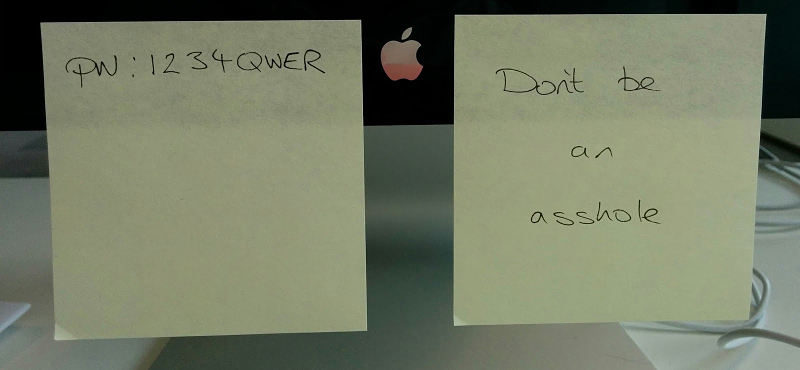
Comments are moderated and will only be visible if they add to the discussion in a constructive way. If you disagree with a point, please, be polite.




Tell us what you think.